cybermad
Clan Leader
- Modelo
- Z3 2.8 / GR86
- Registrado
- 11 Feb 2008
- Mensajes
- 105.998
- Reacciones
- 93.530
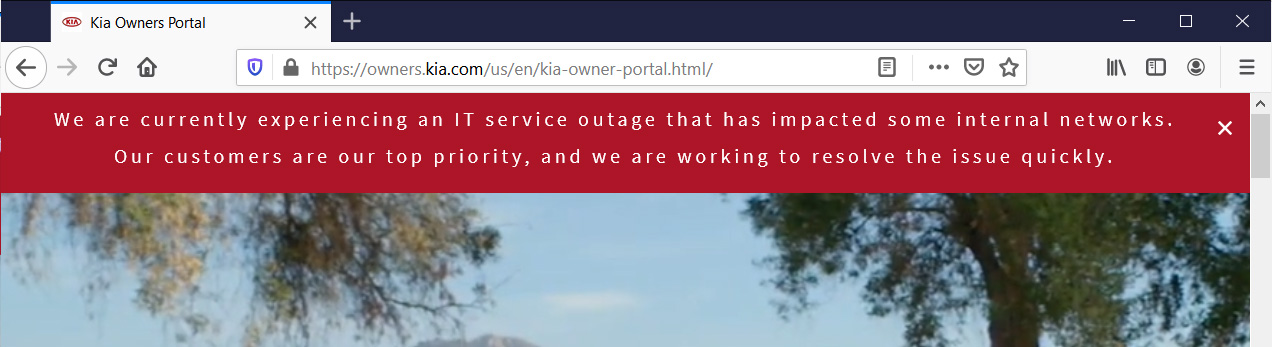
Se informa que Kia sufre un ataque de ransomware con una demanda de 20 millones de dólares
Si Kia no paga, los piratas informáticos darán a conocer los datos robados al público.

ACTUALIZACIÓN: Un aviso anónimo alega que los técnicos del concesionario Hyundai no pueden acceder a parte del sistema para usar equipos de diagnóstico. Este ha sido el caso presuntamente desde el sábado, según la persona que se puso en contacto con nosotros.
Hemos contactado a Hyundai y Kia con estos nuevos detalles para su confirmación.
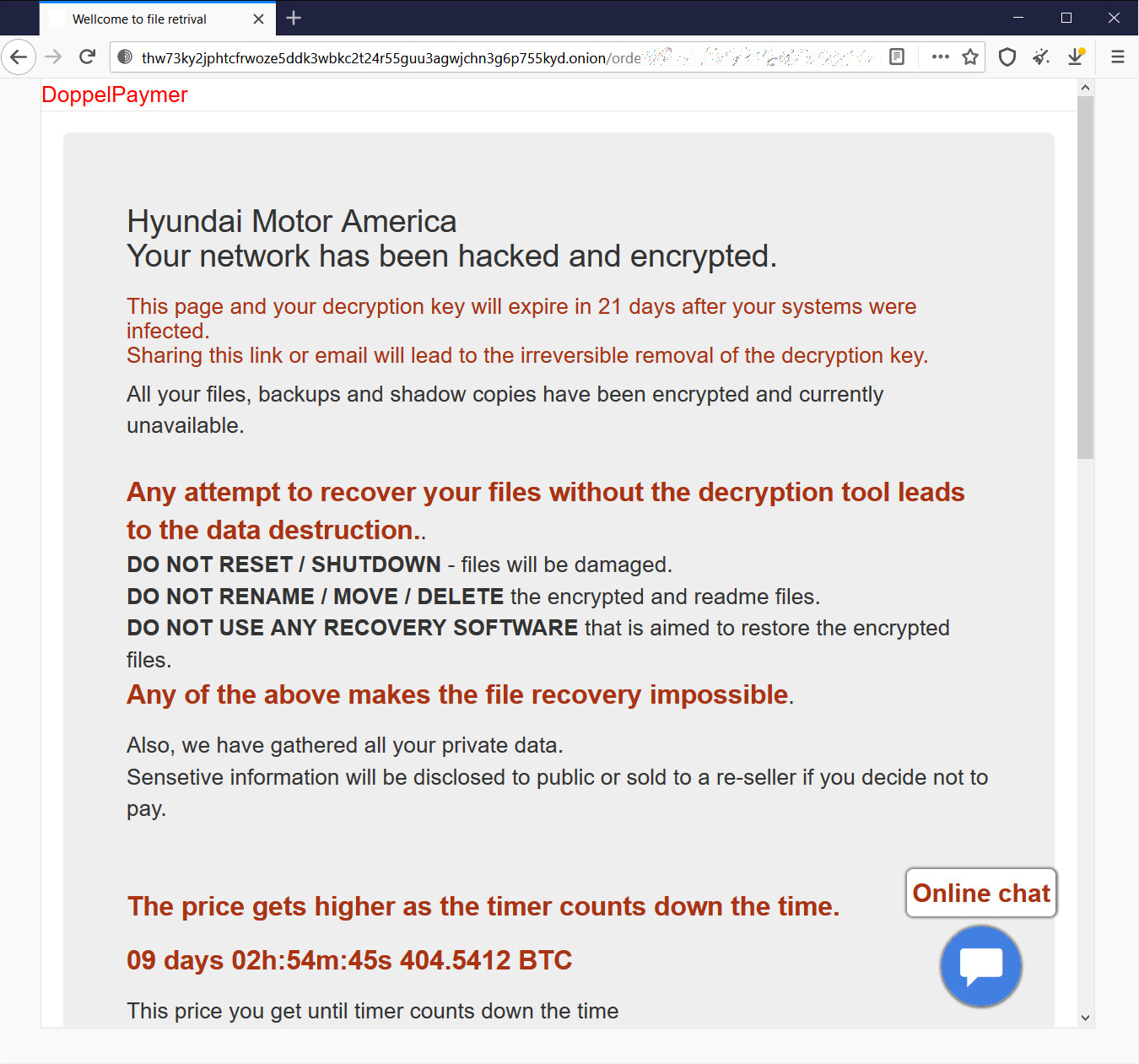
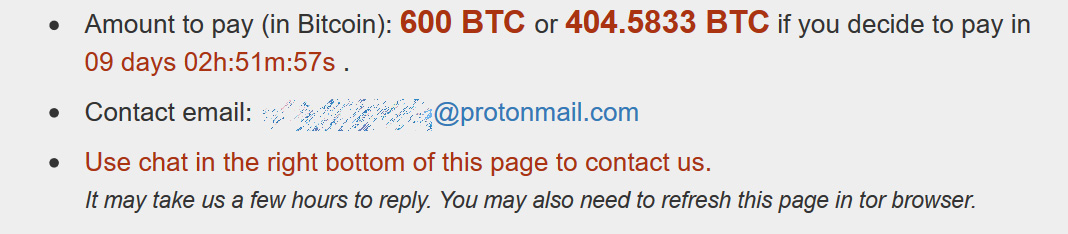
Un grupo de piratas informáticos atacó Kia Motors America y sometió al fabricante de automóviles a un ransomware que supuestamente cerró servicios vitales como sus aplicaciones UVO Link, el sistema de pago y los sitios que usan los distribuidores, según Bleeping Computer . Los piratas informáticos solicitan 404.5833 bitcoins para descifrar los datos y, a los valores actuales, esto equivale a 20.899.559,53 dólares. Si Kia no paga lo suficientemente rápido, entonces el rescate aumenta a 600 bitcoins ($ 30.994.200).
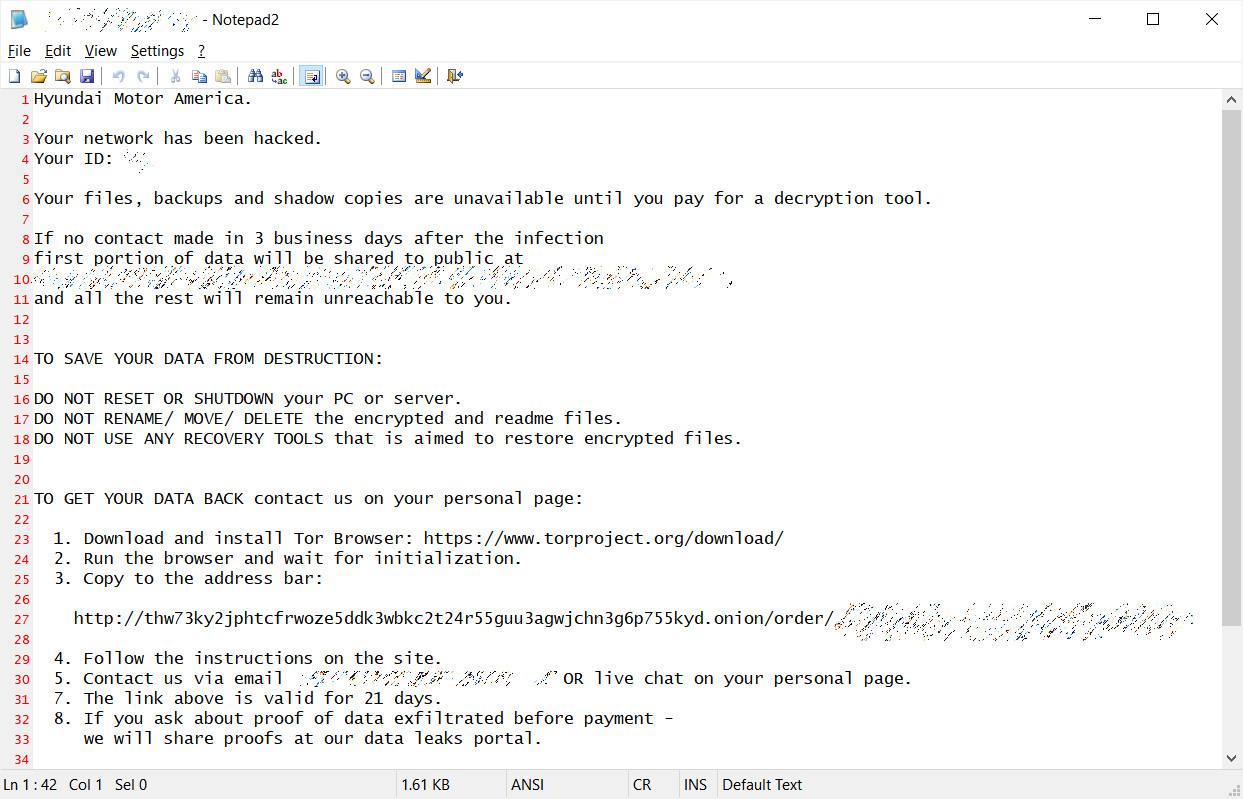
Bleeping Computer también obtuvo la supuesta nota de rescate que los piratas informáticos enviaron a Kia. La carta dice que si Kia no intenta contactar a los atacantes dentro de los tres días, una parte de los datos obtenidos se hará pública. Las demandas no dicen específicamente qué tipo de datos robó este hack.

En una declaración a Bleeping Computer el 17 de febrero, el fabricante de automóviles negó que estuviera sujeto a ransomware. "También somos conscientes de las especulaciones en línea de que Kia está sujeto a un ataque de 'ransomware'. En este momento, podemos confirmar que no tenemos evidencia de que Kia o cualquier dato de Kia esté sujeto a un ataque de 'ransomware'", dice el anuncio. .
Algo extraño es que la carta se dirige a Hyundai Motor America, que está estrechamente relacionada con Kia. En este momento, no parece que Hyundai se vea afectado por el ataque, pero Motor1.com se está comunicando con el fabricante de automóviles para confirmarlo.
A medida que los fabricantes de automóviles utilizan cada vez más la tecnología en red, los ataques de piratería y ransomware se convierten en un mayor riesgo de interrumpir su negocio. Por ejemplo, el ransomware en 2017 obligó a Renault a detener temporalmente la producción en Francia , y Nissan tuvo que hacer lo mismo en el Reino Unido en ese momento

Si Kia no paga, los piratas informáticos darán a conocer los datos robados al público.

ACTUALIZACIÓN: Un aviso anónimo alega que los técnicos del concesionario Hyundai no pueden acceder a parte del sistema para usar equipos de diagnóstico. Este ha sido el caso presuntamente desde el sábado, según la persona que se puso en contacto con nosotros.
Hemos contactado a Hyundai y Kia con estos nuevos detalles para su confirmación.
Un grupo de piratas informáticos atacó Kia Motors America y sometió al fabricante de automóviles a un ransomware que supuestamente cerró servicios vitales como sus aplicaciones UVO Link, el sistema de pago y los sitios que usan los distribuidores, según Bleeping Computer . Los piratas informáticos solicitan 404.5833 bitcoins para descifrar los datos y, a los valores actuales, esto equivale a 20.899.559,53 dólares. Si Kia no paga lo suficientemente rápido, entonces el rescate aumenta a 600 bitcoins ($ 30.994.200).
Bleeping Computer también obtuvo la supuesta nota de rescate que los piratas informáticos enviaron a Kia. La carta dice que si Kia no intenta contactar a los atacantes dentro de los tres días, una parte de los datos obtenidos se hará pública. Las demandas no dicen específicamente qué tipo de datos robó este hack.

En una declaración a Bleeping Computer el 17 de febrero, el fabricante de automóviles negó que estuviera sujeto a ransomware. "También somos conscientes de las especulaciones en línea de que Kia está sujeto a un ataque de 'ransomware'. En este momento, podemos confirmar que no tenemos evidencia de que Kia o cualquier dato de Kia esté sujeto a un ataque de 'ransomware'", dice el anuncio. .
Algo extraño es que la carta se dirige a Hyundai Motor America, que está estrechamente relacionada con Kia. En este momento, no parece que Hyundai se vea afectado por el ataque, pero Motor1.com se está comunicando con el fabricante de automóviles para confirmarlo.
A medida que los fabricantes de automóviles utilizan cada vez más la tecnología en red, los ataques de piratería y ransomware se convierten en un mayor riesgo de interrumpir su negocio. Por ejemplo, el ransomware en 2017 obligó a Renault a detener temporalmente la producción en Francia , y Nissan tuvo que hacer lo mismo en el Reino Unido en ese momento



 no se como habrán salido
no se como habrán salido donde esté la cuartilla y el lápiz...
donde esté la cuartilla y el lápiz...

 Que decidan....
Que decidan....